A recent study has found that over two-thirds of organizations are not confident they have made necessary security improvements to combat attacks like the recent WannaCry and Petya cyber-attacks.
The new research from Tripwire found that in spite of the devastating consequences and damage caused by the WannaCry and Petya attacks, there are still doubts regarding whether organizations have responded appropriately to improve their cyber security defenses.
A third of security practitioners surveyed claim the largest problem their organization faces is establishing what devices are on its network, followed by worries about vulnerability management (14%), administrative privileges (6%), and audit logging (6%). Not surprisingly, 40% of respondents believe there’s no one source to blame and that their business was guilty of all of the above.
Organizations that were lucky enough to not fall victim to the recent cyber-attacks should be grateful it did not happen to them, but more importantly, need to access their cyber defenses and ensure this could not happen to them in the future.
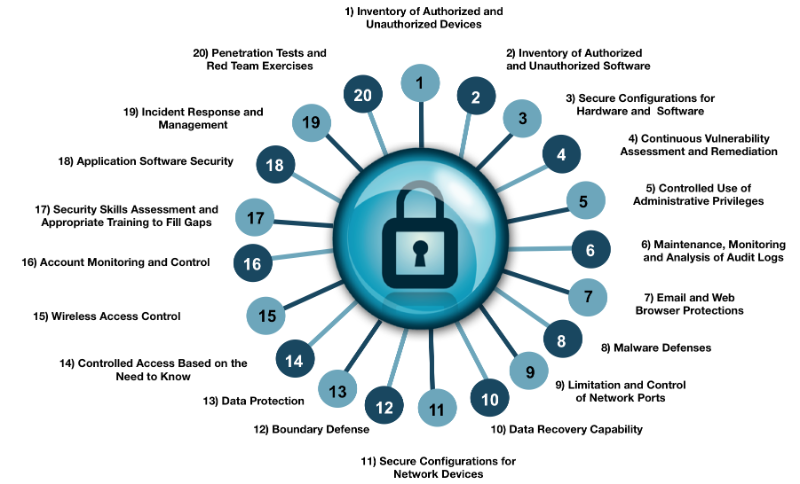
NNT recommends at a base level implementing the CIS Controls. These are a relatively small number of prioritized, well-vetted, and support security actions that organization should take to access and improve their current security state. Developed by security experts from every industry and every role imaginable, these experts pooled together their first-hand knowledge from defending against cyber-attacks to evolve the CIS Controls, representing the best defensive techniques to prevent or track them.
Read this article on InfoSecurity Magazine












